Appendix 1: security and privacy
![]() This page contains information about how to secure IT and a webshop (or website) and how to protect your online privacy. We advise each merchant to take the time to read this document. You will be better protected against cyber attacks and online fraud. The difficulty level is adjusted to the average internet user and the topics are ranked from important to less important.
This page contains information about how to secure IT and a webshop (or website) and how to protect your online privacy. We advise each merchant to take the time to read this document. You will be better protected against cyber attacks and online fraud. The difficulty level is adjusted to the average internet user and the topics are ranked from important to less important.
IT security is a mindset. It takes time and effort, and the results are not immediately visible. It's not a popular topic, but necessary. Unfortunately, we are seeing that many internet users are careless when it comes to online security and privacy. This is the main reason for DDOS attacks and junk e-mail.

Physical (hardware) security
Almost all of the information below will be meaningless if your PC, laptop, tablet or phone is physically accessible.
- Prevent theft: do not leave your devices visibly in a car
- Watch out in crowded places, such as on public transport
Secure your PC and laptop with a password, as well as your phone and tablet with a PIN-code to unlock the screen.
A secure operating system
The operating system is the application that runs all your applications. A secure operating system is fundamental: if the operating system is not secure, then the security of the applications on top of it is trivial.
Approximately 50% of Windows computers are infected with malware. These are small applications that can spy on the user via the microphone and webcam. They are also capable to log keystrokes. Malware can also collect data such as passwords, address books, documents, photos and screen captures. Usually, infected computers are used in a botnet: they attack websites and are used to send spam.
Malware runs in the background and is not visible on the screen. There can be some clues however: the computer or phone will be slower, it will consume more power (note the fan) and it will send more data.
Avoiding Malware
- Do not open .doc, .docx, .exe, .ppt, .pptx, .xls, .xlsx and .zip files on the web and in e-mails.
- Make use of open source software: when the code is freely available, you can be more confident that it has no back doors .
- Keep your operating system, web browser and e-mail application up-to-date.
Junk e-mail (spam)
Incoming e-mail is automatically scanned by our spam filter. When spam is detected, the e-mail is moved to the junk e-mail folder and a warning message is added at the top of the e-mail. We never delete e-mail from our customers: this is to prevent that valid e-mails would be lost.

Outgoing e-mails from your mailbox and from your website include a DKIM signature and SPF records. You can test your e-mail at mail-tester.com.
- Do not reveal your e-mail address on your website; spam bots scan websites for harvesting e-mail addresses.
- Make sure that your e-mail address is difficult to guess, avoid info@mydomain.com.
- Create a temporary e-mail forwarding address for use on websites that you do not trust.
- Use a secure and up-to-date e-mail client or use our webmail.
- Do not open e-mails with attachments if you don't know the sender. Be aware of obvious e-mail scams, such as winning a smartphone, a lottery or an inheritance.
Safe web browsing
Web browser
Browsing the web is done with a web browser: this is the application that you use to view websites. Regularly there are vulnerabilities found in web browsers, so it is important that your browser is up-to-date!
List of web browsers: (sorted by use)
| Browser | Description |
|---|---|
| Google Chrome | Free web browser from Google |
| Mozilla Firefox | Open source web browser from Mozilla |
| Microsoft Internet Explorer | Web browser from Microsoft, replaced by Microsoft EDGE |
| Apple Safari | Web browser from Apple. The Windows version was discontinued in 2012. |
| Microsoft EDGE | Webbrowser from Microsoft, replacing Internet Explorer |
| Opera | Free web browser available for Windows, Mac and Linux |
| Pale Moon | Open source fast web browser based on Mozilla Firefox |
| Chromium | Open source web browser which Google Chrome is based on |
Browser add-ons
Browser add-ons (plugins or extensions) can improve your security and privacy on the internet.
- NoScript
- NoScript blocks scripting that follows you on the web. Reliable websites can be whitelisted. Javascript is commonly used for tracking your activity on a website. This add-on is advised!
- Self-Destructing Cookies
- Cookies are often used (or abused) to follow you on the web. Self-Destructing Cookies is an add-on that automatically deletes cookies after your visit to the website.
- HTTP referer
- When you visit a web page, the HTTP referer is sent: this is the address of the previous page that you visited. This way, websites know from which website you arrived. If you do not want this, it can be disabled with the Change Referer Button.
Advertisements
You are reading an article online, but the website is stuffed with flashing ads which distract you from the actual content. Ads are not only disturbing, in many cases, they also track which websites you visit and what content interests you. An efficient way of preventing this is the blocking of ads and tracking via the HOSTS file. This can be installed on your PC, but also, for example, on your router. This way, your entire network is protected.
An additional advantage: because the ads are not downloaded, you save data and web browsing goes a lot faster.
Website security
All our webshops are secured with an ![]() SSL/TLS certificate. This is automatically installed when you register a domain name. You don't have to do any technical installations yourself.
SSL/TLS certificate. This is automatically installed when you register a domain name. You don't have to do any technical installations yourself.
Website apps such as widgets, scripting, connectors to social media or a visitors counter can make your website slower, rise security concerns and can track your visitors. We recommend to use them with care or make no use of them at all.
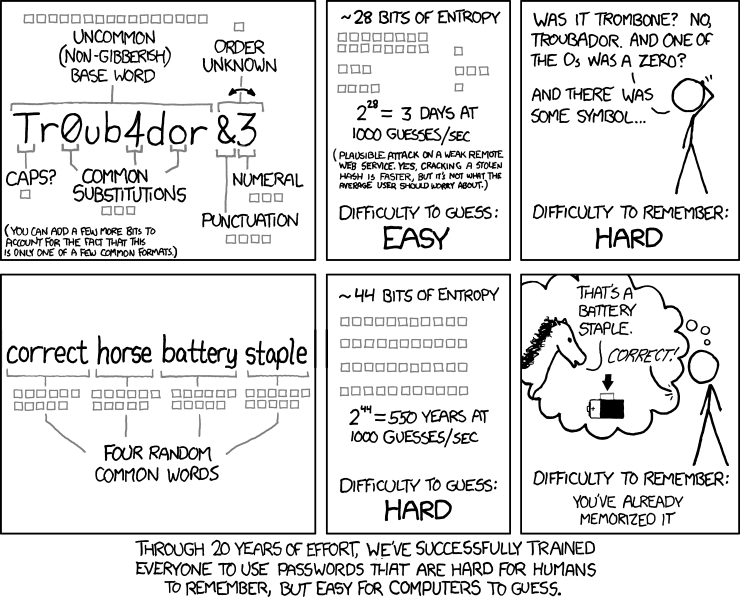
Choosing a good password
Password do's
The ideal password is consists of:
- At least 12 to 14 characters
- Regular letters and capital letters
- One or multiple symbols
- Multiple words
Tip: use a passphrase. It's easier to remember and it's safer due to the large number of characters.
Most web browsers will help you to remembering your passwords. This is a fairly safe method, provided that your device is secure and that a "master password" is set: this master password can unlock all your other passwords.
Password dont's
- Do not use your date of birth, the name of your partner or the name of your pet.
- Do not use a single word, from any language, even not combined with numbers.
- Avoid to use a year number, especially at the end of the password.
- Do not use the same password in multiple places.
- Do not send your password, not by phone, via e-mail, via social media or via messenger.
- Some websites use a system with a number of personal questions as a password recovery. Avoid using this method. If someone who wants to break into your account, they will usually try this way first. A lot of personal information can be found on social media.
Password myths
- Frequently changing your password is not necessary.
- Writing down a password is ok, on the condition that it is kept in a safe place. So no post-its on the screen!
Two factor authentication
Many web-based services, including EasyWebshop, offer two factor authentication. This provides extra security when logging in. The security is based on something you know (your password) and something you have (your phone).
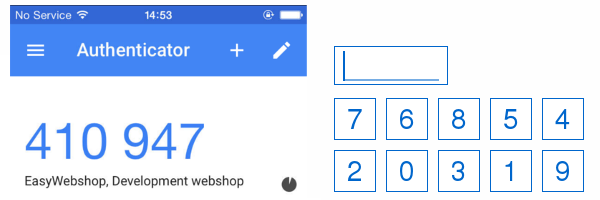
We highly recommend this: the extra security makes it a lot more difficult for attackers to get access to your account.
Payment fraud
Payment withdrawal (Chargeback, issuing a refund)
In case of payments with credit card and PayPal, the consumer has the possibility to withdraw the payment. Unfortunately, it happens that customers withdraw their payment after they received your products or services. In this case, it is up to you to prove that there is effectively delivered in order to still receive the payment.

Payments that can be withdrawed are:
- Credit cards (Visa / MasterCard)
- PayPal
Payments that cannot be undone:
- Bank transfer
- Bancontact / Mistercash
- Bitcoin and other cryptocurrencies
- iDEAL
- Maestro
- Sofortbanking
You can add a surcharge for some payment options to compensate for the loss caused by fraudulent transactions and administration costs. Make sure that your customers can choose at least one payment option for which they are not required to pay extra.
Some payment providers collect personal information from consumers in order to create a spendings profile. To protect the privacy of your customers, we only send the data that a payment provider needs to process the payment:
| Data | Example |
|---|---|
| Order code | 20160-17140-65236-59629 |
| Desired method of payment | Bitcoin, PayPal, Sofort |
| Total price | 3.95 |
| Currency | BTC, EUR, USD |
| Interface language | Dutch, English, Spanish |
False proof of payment
It sometimes happens that customers firmly claim that they paid their order, or that they want to have their product fast and do not want wait for the bank transfer to complete. Be aware that a bank statement can easily be photoshopped.
- Wait until the money is in your account.
- A phone call to your payment provider or bank can confirm whether the payment has been made.
For webshops, especially in sales to consumers, it is customary to send the products after the payment is received.
Domain name fraud
Typical spam e-mails to online merchants are false invoices or reminders to renew your domain name. The only valid emails for your domain name are the emails from EasyWebshop and from the registry's:
- DENIC, Germany
- DNS Belgium
- EURid
- ICANN
- SIDN, the Netherlands
Customers with threats or with unrealistic demands
This situation occurs especially to new merchants: fraudsters are well aware of the regulations and try to scam the merchant. They target webshops that have just started.

- A product is not priced or priced too low, the customer demands that you do sell it anyway.
- A particular clause is not in the terms and conditions, a customer tries to blackmail the merchant.
- The return of used products.
Customers can threat with a lawsuit, or the posting of negative reviews on internet forums or social media.
- Make sure that your terms and conditions are set correctly for the country in which you sell.
- Obtain legal advice when necessary.
- Don't give in to threats and blackmail. Avoid emotional reactions.
- Respond positively to negative reviews.
Payed removal of negative reviews
There are review sites where customers can post reviews about your webshop. This can be an added value to your webshop, but unfortunately these reviews do not always reflect the reality. Satisfied customers usually do not place reviews, an excellent service is - correctly - considered to be normal.
It becomes a problem when these 1% of dissatisfied or unrealistic customers place negative reviews. Some review sites exploit this by forcing you to sign an expensive subscription to be able to remove or to answer the reviews. Do not accept this.
False marketing promises
Starting a business and/or a webshop goes slowly: you will have few customers in the beginning. Advertising and marketing can help you acquiring your first customers. Be aware that there are marketing companies that promise a lot but fail to fulfill.

Some typical situations:
The smooth marketing boy always uses the right words: you are going to be rich! His enthusiasm and speech charm you, he has the perfect solution for your business. You only have to sign and new customers will be flooding in. A few weeks later, when your enthusiasm has calmed down, it all seems to be untrue.
- Try to obtain an agreement where you only pay per provisioned customer.
Rogue marketing companies may send you a form to add you to their business directory. Coincidentally, there is a mistake in your business's name or in the address. When you send the improved version back, you actually commit to an expensive subscription that is difficult to cancel. The business directory provides little or no customers.
- Read the small print.
Even large (media)companies can do similar scams. An ad in the newspaper, a magazine or a commercial on the radio: it may be expensive without providing the expected results.
- Ask for references, call the current advertisers and ask if they are satisfied with the result.
Social engineering
The actual user is, in many cases, the weakest link in IT security. Cyber criminals use crafty tricks to draw information from you. They will, for example, ask you to visit a website infected with malware, or with a web form where you have to log in. The credentials are then sent to the cyber criminal. Or you receive a phone call in which your password or authentication code is asked.
They pretend to be an employee of a bank or an online service or even the police. These e-mails or phones can be very enthusiastic and convincing. You can have both men and women on the line, in many cases English speaking people. Be on your guard, especially when you did not ask for anything!
List of security and privacy tips
The tips below can offer extra security and privacy. They are ranked from "highly recommended" to "paranoia".
Avoid apps on the smartphone. Be aware that apps can have access to your photos, camera, microphone, and can send data. If you use them anyway, try to limit access to your personal information.
Avoid unencrypted forms of communication or closed encryption protocols such as Skype and WhatsApp. Good alternatives are e-mail (PGP), XMPP, Ring.cx and Tox.
The Internet of Things (IoT): a coffee machine that is connected to the internet, a smart TV with built-in microphone: it is disastrous for your privacy.
Secure your Wi-Fi network with a strong password and WPA2. Change the admin password of your router. Only make a connection to a Wi-Fi network with WPA2 security and avoid unencrypted networks in hotels or public places. Routers may contain malware in their firmware, you can replace it with DD-WRT or OpenWrt.
Many search engines track what you search, and link it to you as a person. Search engines that you do not follow are DuckDuckGo and StartPage.
For optimal security, encrypt your hard drive. When your laptop is stolen the data cannot be read without the password. A BIOS password does not protect the data on the hard disk!
Virus scanners are not as effective as supposed. In many cases, they make your computer slower and in some cases they contain even malware. A secure operating system with a firewall prevents that you are vulnerable.
Create back-ups and store your backups offline. Test whether you can later restore the backup. External hard drives are a handy tool for this.
Turn off Bluetooth, Wi-Fi and 3G/4G when not in use. Shield RFID tags. Give preference to a wired keyboard.
Tape off your webcam. A lot of malware can activate the camera in your laptop, tablet or phone without illuminating the camera LED. With a piece of cardboard in between you can prevent that glue sticks to the lens of your camera.
Give preference to paying with cash over debit cards and credit cards. This way you avoid that a profile of your purchases is created.
Using the DNS servers, information about the websites you visit can leak. If you want to avoid this, choose a DNS service that you trust or use a VPN.
Next page: Appendix 2: application limits
- Introduction
- Product management
- Online store configuration
- Account and shop settings
- Payment methods and Payment Service Providers
- Invoices and Terms & Conditions
- Setting shipping costs
- Discounts and surcharges
- Registering and transferring domain names
- Multilingual shop
- Connecting to external platforms
- Personalized web addresses
- Managing multiple webshops (Multishop)
- Automatic emails to customers
- Designing a beautiful layout
- Order management
- Marketing
- Modules
- Backups and exporting data
- Email and web mail
- Administrator accounts
- High quality photos
- Two-factor authentication
- Labels
- Meta tags - Website verification
- Live chat
- Slideshow
- Visitor analysis - Google Analytics
- Filters
- Point Of Sale (POS)
- Form fields
- Digital or virtual products
- Symcalia reservation system
- Guestbook
- Contacting the helpdesk
- Appendix 1: security and privacy
- Appendix 2: application limits
